Blogs Troubled by Man in the Middle Compromises

Adfolks
Techie Nuggets,
Troubled by Man in the Middle Compromises
Posted:
As an IT administrator, you are well aware of man-in-the-middle (MITM) attacks and their repercussions on your organization.
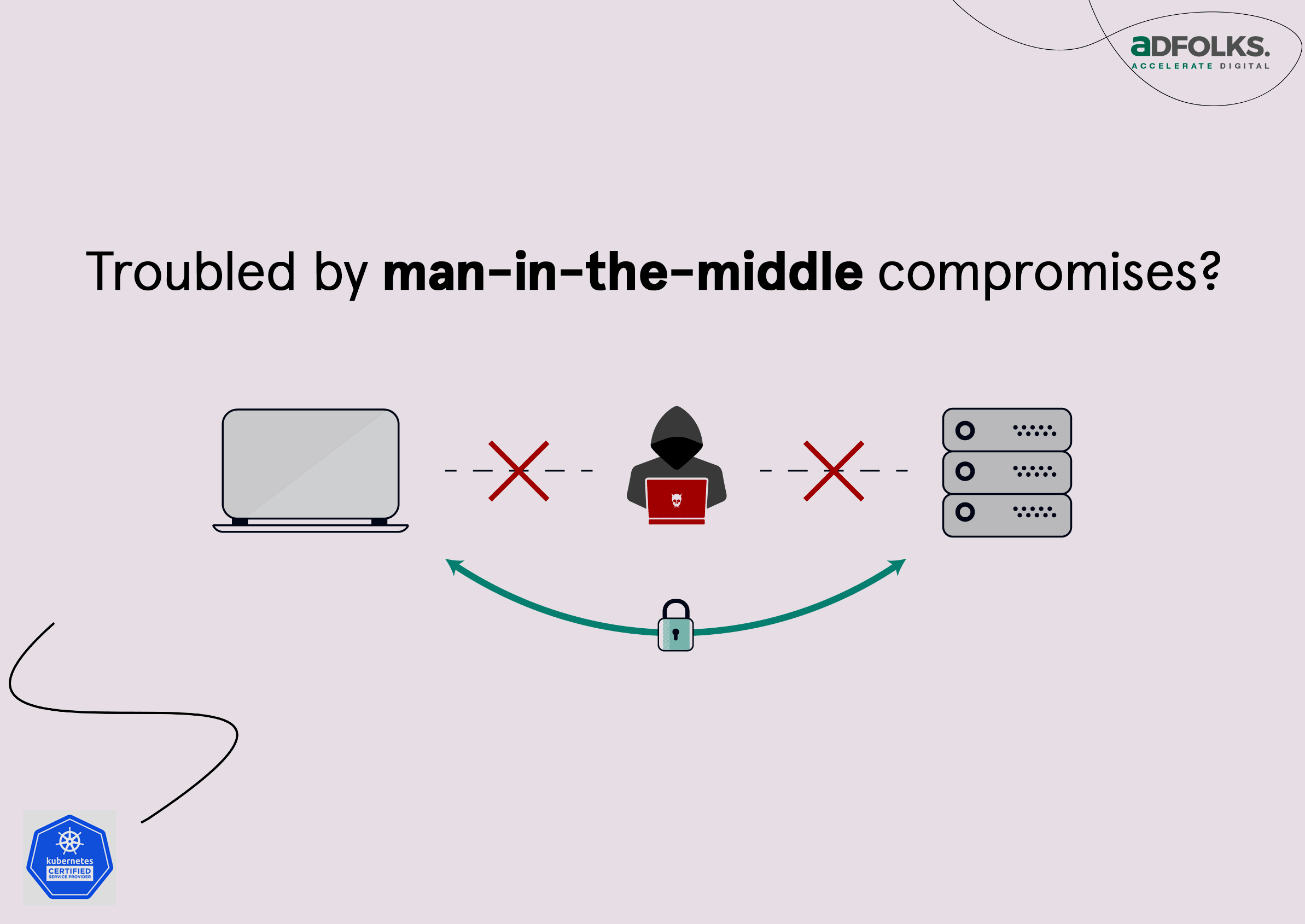
Take these steps to mitigate these potential threats:
- High chances of risk if the cluster is shared among multiple teams/tenants/environments.
- Apply a policy that ensures no ClusterIP service that contains an external IP’s spec can ever be created. This approach eliminates the ability to divert traffic to an external IP address.
- While adopting Kubernetes, make sure that an admission controller webhook is implemented to ensure that every namespace’s service account is scoped to a role that does not allow PATCH requests to the LoadBalancer service.
- Look out for tools that can identify whenever a service is accessing an external IP address.
- Be wary, if your organizations continue to run older versions of Kubernetes clusters since, if left unattended, it could become a significant problem.
- Ensure the use of two-way SSL for critical service apps.
- Finally, always make sure that the cluster is hardened/audited before public ACL.
For more queries on MITM and other Kubernetes-related vulnerabilities, reach out to our team